A fresh month, a fresh security problem. Today Intel disclosed "Special Register Buffer Data Sampling" (or SRBDS) which has been named CrossTalk by a bunch of researchers from VUSec. This is just another in the growing list of security problems Intel has suffered over the last few years.
For the first time this enables clever attackers to leak sensitive information across cores on many different generations on Intel CPUs, bypassing previous security fixes against previous issues like Spectre and Meltdown. You can see a list of affected CPUs here, it's unfortunately quite a large list covering a huge amount of Intel's different CPU brands.
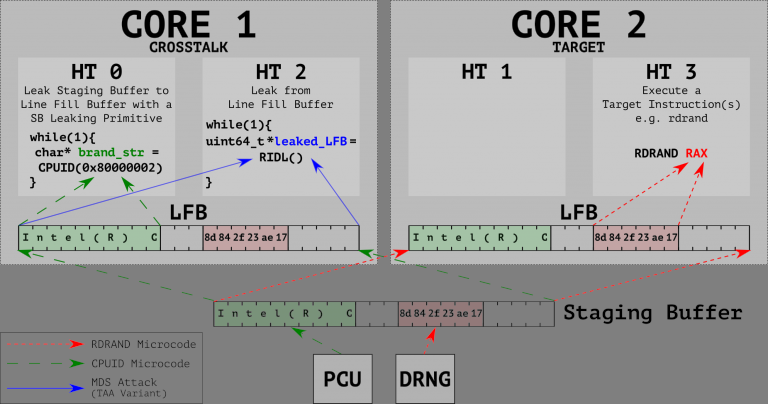
The VUSec team built a profiler called CrossTalk, allowing them to inspect "the behavior of complex (“microcoded”) x86 instructions beyond the CPU core boundaries". Using it they found an undocumented "staging buffer" that contained a bunch of sensitive data (including that from the random number generator) that can be leaked across cores using MDS style attacks.
With responsible disclosure, the team told Intel of the issues back in September 2018, followed by more information in July 2019 and Intel rewarded them with the Intel Bug Bounty (Side Channel) Program. Intel requested it be under embargo until now, due to the difficulty of a fix.
There's microcode updates going out from Intel to clean up SRBDS, with Intel now locking the whole memory bus before it talks to the staging buffer and will only unlock it after clearing it. This way nothing should be exposed across cores. How's performance loss with it? Considerable apparently so Intel has only applied the fix to a few security instructions: RDRAND, RDSEED, and EGETKEY. Phoronix did a quick test and it's quite dramatic.
You can see the official Intel release here and the VUSec CrossTalk info dive here.
Quoting: HoriIntel-based PCs really do slow down over time, don't they?
It's converging towards a Z80 performance wise.
Getting close.
Quoting: HoriIntel-based PCs really do slow down over time, don't they?
i still like my old i5 6500. i cant say it got slower.
very low power consumption.
but today i wouldnt buy intel. too hot, too much power consumption, too expensive... and new security problems
Last edited by mylka on 10 June 2020 at 12:39 am UTC




See more from me